The Challenge
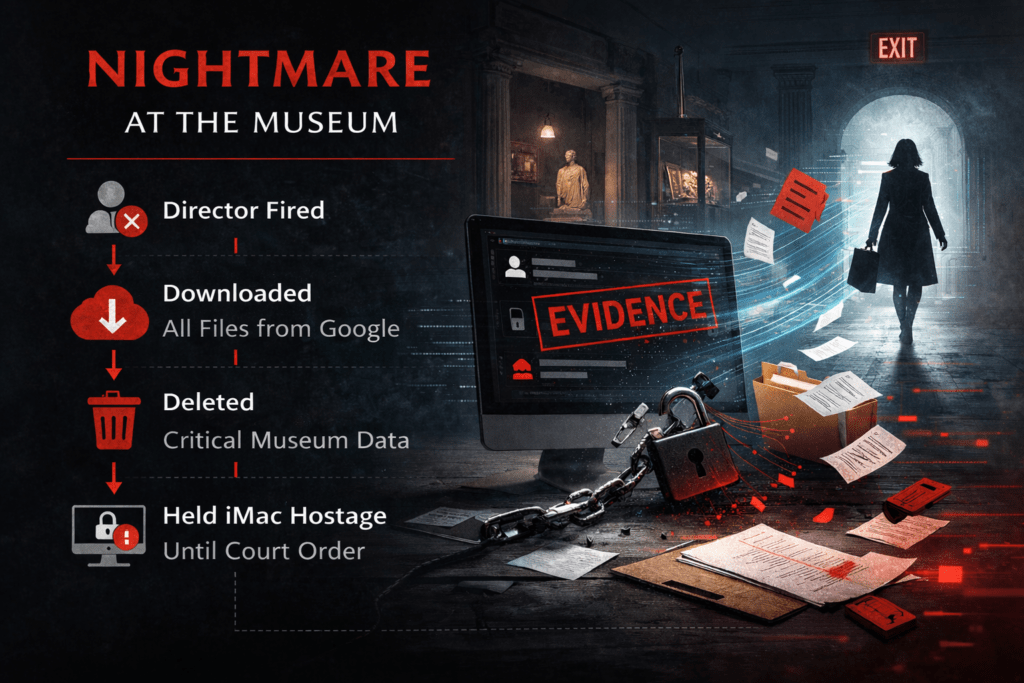
A history museum faced a high-risk insider incident after the Director of Operations was terminated for misconduct. Within days, critical Google Workspace data was stolen and deleted, disrupting operations and creating legal exposure.
What Happened
The museum’s Director of Operations was terminated for misconduct and had their access scheduled for offboarding. Shortly after the termination, the museum noticed unusual activity tied to the former director’s Google Workspace account. Over a short window of time, the former director signed in and began pulling down large volumes of data from Google Drive, including operational documents and internal files the museum relied on day to day. After downloading the data, she deleted those same files from Google
Workspace, leaving staff scrambling as folders and documents suddenly disappeared. Because this was an insider incident, the museum needed more than suspicion. They needed a clear, provable timeline showing it was her account, her logins, and her actions that led to the download and deletion of the files.
Why It Matters
When the threat is internal, intent is harder to dispute, and evidence must be airtight. This is where most cases fail, because “we think it was her” does not hold up in court.
Gipson Cyber’s Response:
→ Pulled and preserved audit logs
→ Correlated logins, devices, & IPs
→ Built a clear timeline of activity
The Outcome
- Confirmed attribution with evidence
- Supported the museum’s legal action
- Tightened offboarding controls
- Former employee prosecuted