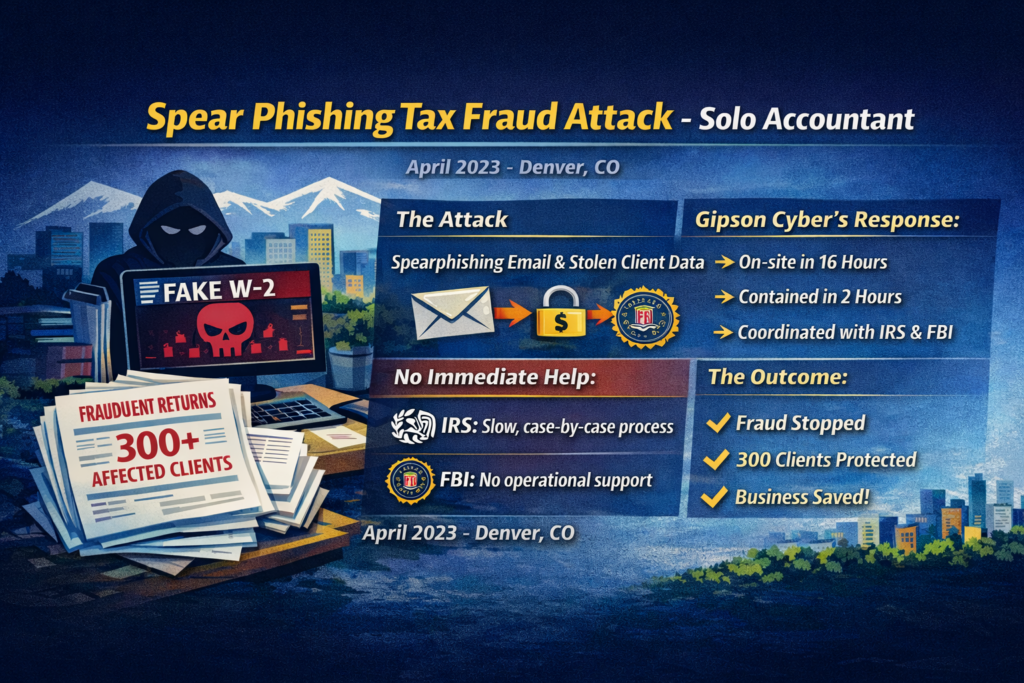
The Challenge A solo accountant discovered that cyber criminals had gained access to their environment and client records. Within days, the impact escalated into a tax-fraud event affecting 300 clients. What Happened In April 2023, outside Denver, CO, a solo accountant was targeted by a spearphishing email containing a fake W-2 PDF. Once opened, the […]
Category Archives: Use Cases
The Challenge Impersonator accounts began appearing across social media, posing as senior US Central Command generals and posting false, inflammatory statements. The goal was clear: create confusion, damage trust, and spark headlines before anyone could verify the source. What Happened Impersonators created realistic lookalike accounts posing as U.S. Central Command leadership, using copied photos, bios, […]
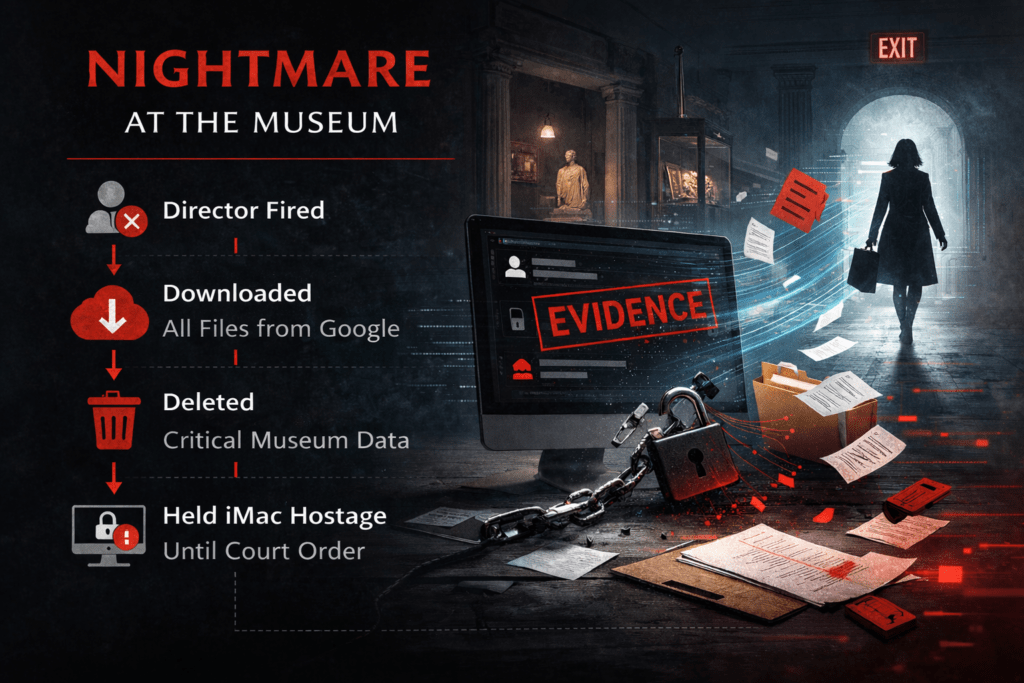
The Challenge A history museum faced a high-risk insider incident after the Director of Operations was terminated for misconduct. Within days, critical Google Workspace data was stolen and deleted, disrupting operations and creating legal exposure. What Happened The museum’s Director of Operations was terminated for misconduct and had their access scheduled for offboarding. Shortly after […]
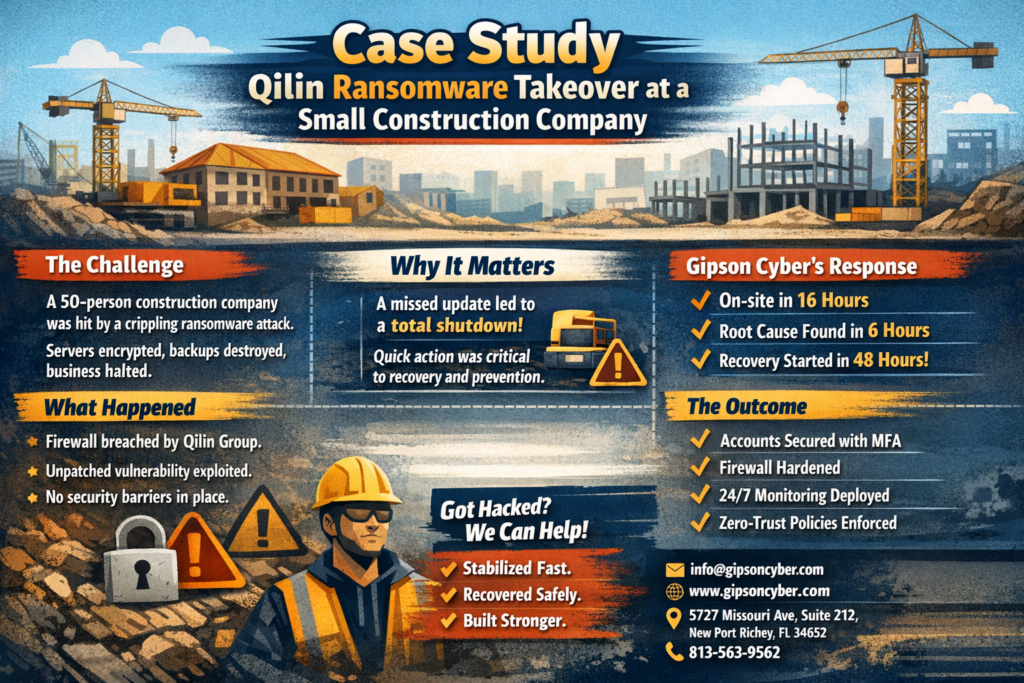
The Challenge A 50-person construction company experienced a sudden, company-wide ransomware attack that halted business operations. Core servers and virtual machines were encrypted, administrator access was lost, and backups were rendered unusable. What Happened The attacker got in through the company’s internet firewall. A missed security update exposed a remote access vulnerability, allowing the attacker […]
The Challenge A new client was mid-onboarding when our SIEM lit up with suspicious traffic, and our EDR flagged suspicious admin activity tied to the Domain Controller (DC). This was not “new environment noise.” This was “someone has the keys to the kingdom” noise. What Happened During the investigation, we uncovered something worse than a […]
The Challenge A 15-person law firm was dealing with nonstop fraudulent bank and credit card activity. They had cybersecurity monitoring through their MSP, but the MSP’s anti-virus was inadequate and failed to detect the threat. The firm tried to contain the damage by changing bank accounts and credit card numbers multiple times, but the fraud […]